Prerequisites
Before starting, make sure you have the following installed on the machine where the agent will run:Step 1 — Open the WCF Installation Page
Navigate to the WCF installation page in the OneFirewall portal (please, refer to your on premises installation): https://app.onefirewall.com/install-wcf.htmlStep 2 — Select FortiCloud
On the integration page, select FortiCloud from the list of available connectors.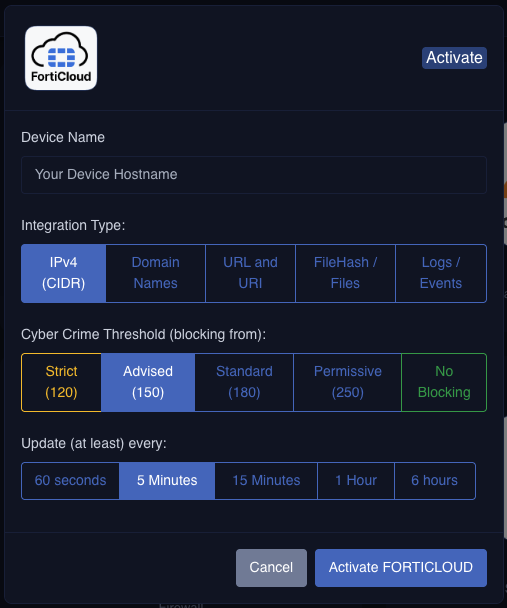
Step 3 — Configure the Integration
Fill in the required fields:| Field | Description |
|---|---|
| Device Name | A unique name to identify this device within OneFirewall |
| Type | Select IPv4 |
| Score | Set the threat score threshold to use for filtering |
| Update Time | How often the agent fetches updated data (e.g. every 5 minutes) |
Setting the update time to 5 minutes is recommended for near-real-time threat intelligence updates.
Step 4 — Activate FortiCloud
Once all fields are filled in, click the Activate FORTICLOUD button. After activation, OneFirewall will generate a ready-to-usedocker-compose.yml file with all the required environment variables pre-populated for your account.
Step 5 — Deploy with Docker Compose
The generated docker-compose.yml
Your configuration file will look like the following:
docker-compose.yml
The environment variables (e.g.
OFA_JWT_TOKEN, AGID) are automatically filled in by OneFirewall after you click Activate FORTICLOUD.The environment variables
FORTINET_API_KEY, EP_ID are instead the parameters of your API_KEY on FortiAppSec application, and the EP_ID is the application ID and should be configured from your organization values.Start the agent
Save the generateddocker-compose.yml to a directory on your machine, then run:
Verify the Agent is Running
To check that the container started correctly, run:fortiappsec-updater listed with a status of Up.
To view live logs:
Troubleshooting
Container exits immediately after starting
Container exits immediately after starting
Check the logs with
docker logs fortiappsec-updater. A missing or invalid environment variable is the most common cause — make sure you copied the exact docker-compose.yml generated after activation.Cannot pull the Docker image
Cannot pull the Docker image
Make sure Docker is authenticated with the OneFirewall registry. Contact support if you receive a
403 Forbidden or unauthorized error when pulling the image.Threat data is not updating
Threat data is not updating
Verify the container is running and check that the
OFA_JWT_TOKEN is still valid. Tokens may expire — re-activating the integration on the portal will issue a new token.
